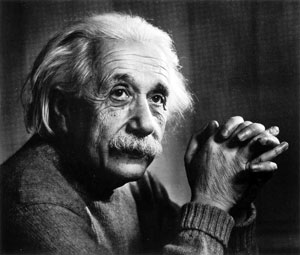
Einstein’s Secret to Amazing Problem Solving
(and 10 Specific Ways You Can Use It)
I have always had a soft spot for Einstein. He died at exactly the same time I was born and unknowingly, muntil recently, I have been using his quotes all my life, That is sadly where our similarities end, Did I also ever tell you that I quote Sherlock Holmes too…………….
Einstein is quoted as having said that if he had one hour to save the world he would spend fifty-five minutes defining the problem and only five minutes finding the solution.
This quote does illustrate an important point: before jumping right into solving a problem, we should step back and invest time and effort to improve our understanding of it. Here are 10 strategies you can use to see problems from many different perspectives and master what is the most important step in problem solving: clearly defining the problem in the first place!
The Problem Is To Know What the Problem Is
The definition of the problem will be the focal point of all your problem-solving efforts. As such, it makes sense to devote as much attention and dedication to problem definition as possible. What usually happens is that as soon as we have a problem to work on we’re so eager to get to solutions that we neglect spending any time refining it.
What most of us don’t realise — and what supposedly Einstein might have been alluding to — is that the quality of the solutions we come up with will be in direct proportion to the quality of the description of the problem we’re trying to solve. Not only will your solutions be more abundant and of higher quality, but they’ll be achieved much, much more easily. Most importantly, you’ll have the confidence to be tackling a worthwhile problem.
Problem Definition Tools and Strategies
The good news is that getting different perspectives and angles in order to clearly define a problem is a skill that can be learned and developed. As such, there are many strategies you can use to perfect it. Here are the 10 most effective ones I know.
1. Rephrase the Problem
When a Toyota executive asked employees to brainstorm “ways to increase their productivity”, all he got back were blank stares. When he rephrased his request as “ways to make their jobs easier”, he could barely keep up with the amount of suggestions.
Words carry strong implicit meaning and, as such, play a major role in how we perceive a problem. In the example above, ‘be productive’ might seem like a sacrifice you’re doing for the company, while ‘make your job easier’ may be more like something you’re doing for your own benefit, but from which the company also benefits. In the end, the problem is still the same, but the feelings — and the points of view — associated with each of them are vastly different.
Play freely with the problem statement, rewording it several times. For a methodic approach, take single words and substitute variations. ‘Increase sales’? Try replacing ‘increase’ with ‘attract’, ‘develop’, ‘extend’, ‘repeat’ and see how your perception of the problem changes. A rich vocabulary plays an important role here, so you may want to use a thesaurus or develop your vocabulary.
2. Expose and Challenge Assumptions
Every problem — no matter how apparently simple it may be — comes with a long list of assumptions attached. Many of these assumptions may be inaccurate and could make your problem statement inadequate or even misguided.
The first step to get rid of bad assumptions is to make them explicit. Write a list and expose as many assumptions as you can — especially those that may seem the most obvious and ‘untouchable’.
That, in itself, brings more clarity to the problem at hand. But go further and test each assumption for validity: think in ways that they might not be valid and their consequences. What you will find may surprise you: that many of those bad assumptions are self-imposed — with just a bit of scrutiny you are able to safely drop them.
For example, suppose you’re about to enter the restaurant business. One of your assumptions might be ‘restaurants have a menu’. While such an assumption may seem true at first, try challenging it and maybe you’ll find some very interesting business models (such as one restaurant in which customers bring dish ideas for the chef to cook, for example).
3. Chunk Up
Each problem is a small piece of a greater problem. In the same way that you can explore a problem laterally — such as by playing with words or challenging assumptions — you can also explore it at different “altitudes”.
If you feel you’re overwhelmed with details or looking at a problem too narrowly, look at it from a more general perspective. In order to make your problem more general, ask questions such as: “What’s this a part of?”, “What’s this an example of?” or “What’s the intention behind this?”.
Another approach that helps a lot in getting a more general view of a problem is replacing words in the problem statement with hypernyms. Hypernyms are words that have a broader meaning than the given word. (For example, a hypernym of ‘car’ is ‘vehicle’). A great, free tool for finding hypernyms for a given word is WordNet (just search for a word and click on the ‘S:’ label before the word definitions).
4. Chunk Down
If each problem is part of a greater problem, it also means that each problem is composed of many smaller problems. It turns out that decomposing a problem in many smaller problems — each of them more specific than the original — can also provide greater insights about it.
‘Chunking the problem down’ (making it more specific) is especially useful if you find the problem overwhelming or daunting.
Some of the typical questions you can ask to make a problem more specific are: “What are parts of this?” or “What are examples of this?”.
Just as in ‘chunking up’, word substitution can also come to great use here. The class of words that are useful here are hyponyms: words that are stricter in meaning than the given one. (E.g. two hyponyms of ‘car’ are ‘minivan’ and ‘limousine’). WordNet can also help you finding hyponyms.
5. Find Multiple Perspectives
Before rushing to solve a problem, always make sure you look at it from different perspectives. Looking at it with different eyes is a great way to have instant insight on new, overlooked directions.
For example, if you own a business and are trying to ‘increase sales’, try to view this problem from the point of view of, say, a customer. For example, from the customer’s viewpoint, this may be a matter of adding features to your product that one would be willing to pay more for.
Rewrite your problem statement many times, each time using one of these different perspectives. How would your competition see this problem? Your employees? Your mom?
Also, imagine how people in various roles would frame the problem. How would a politician see it? A college professor? A nun? Try to find the differences and similarities on how the different roles would deal with your problem.
6. Use Effective Language Constructs
There isn’t a one-size-fits-all formula for properly crafting the perfect problem statement, but there are some language constructs that always help making it more effective:
Assume a myriad of solutions. An excellent way to start a problem statement is: “In what ways might I…”. This expression is much superior to “How can I…” as it hints that there’s a multitude of solutions, and not just one — or maybe none. As simple as this sounds, the feeling of expectancy helps your brain find solutions. Make it positive. Negative sentences require a lot more cognitive power to process and may slow you down — or even derail your train of thought. Positive statements also help you find the real goal behind the problem and, as such, are much more motivating.
For example: instead of finding ways to ‘quit smoking’, you may find that ‘increase your energy’, ‘live longer’ and others are much more worthwhile goals.
Frame your problem in the form of a question. Our brain loves questions. If the question is powerful and engaging, our brains will do everything within their reach to answer it. We just can’t help it: Our brains will start working on the problem immediately and keep working in the background, even when we’re not aware of it.
If you’re still stuck, consider using the following formula for phrasing your problem statement:
“In what ways (action) (object) (qualifier) (end result)?”
Example: In what ways might I package (action) my book (object) more attractively (qualifier) so people will buy more of it (end result)?
7. Make It EngagingIn addition to using effective language constructs, it’s important to come up with a problem statement that truly excites you so you’re in the best frame of mind for creatively tackling the problem. If the problem looks too dull for you, invest the time adding vigor to it while still keeping it genuine. Make it enticing. Your brain will thank (and reward) you later.
One thing is to ‘increase sales’ (boring), another one is ‘wow your customers’. One thing is ‘to create a personal development blog’, another completely different is to ‘empower readers to live fully’.
8. Reverse the Problem One trick that usually helps when you’re stuck with a problem is turning it on its head.
If you want to win, find out what would make you lose. If you are struggling finding ways to ‘increase sales’, find ways to decrease them instead. Then, all you need to do is reverse your answers. ‘Make more sales calls’ may seem an evident way of increasing sales, but sometimes we only see these ‘obvious’ answers when we look at the problem from an opposite direction.
This seemingly convoluted method may not seem intuitive at first, but turning a problem on its head can uncover rather obvious solutions to the original problem.
9. Gather Facts
Investigate causes and circumstances of the problem. Probe details about it — such as its origins and causes. Especially if you have a problem that’s too vague, investigating facts is usually more productive than trying to solve it right away.
If, for example, the problem stated by your spouse is “You never listen to me”, the solution is not obvious. However, if the statement is “You don’t make enough eye contact when I’m talking to you,” then the solution is obvious and you can skip brainstorming altogether. (You’ll still need to work on the implementation, though!)
Ask yourself questions about the problem. What is not known about it? Can you draw a diagram of the problem? What are the problem boundaries? Be curious. Ask questions and gather facts. It is said that a well-defined problem is halfway to being solved: I would add that a perfectly-defined problem is not a problem anymore.
10. Problem-Solve Your Problem Statement
I know I risk getting into an infinite loop here, but as you may have noticed, getting the right perspective of a problem is, well, a problem in itself. As such, feel free to use any creative thinking technique you know to help. There are plenty to choose from:
Of course, how much effort you invest in defining the problem in contrast to how much effort you invest in solving your actual problem is a hard balance to achieve, though one which is attainable with practice.
Personally, I don’t think that 55 minutes of defining a problem versus 5 minutes acting on it is usually a good proportion. The point is that we must be aware of how important problem defining is and correct our tendency to spend too little time on it.
In fact, when you start paying more attention to how you define your problems, you’ll probably find that it is usually much harder than solving them. But you’ll also find that the payoff is well worth the effort.


 5 Things You Didn’t Know About Cloud
5 Things You Didn’t Know About Cloud